Prepared by the Research Department at lawionyrs
Under the Supervision of Muayid Uldin Malli
Is Smart Contract Exploitation the Most Dangerous Legal Threat Facing the Decentralized Economy?
Introduction
On March 14, 2026, a decentralized finance platform announced that it had suffered a cyberattack resulting in the withdrawal of millions of dollars within minutes due to the exploitation of a software vulnerability inside a smart contract responsible for transaction management. Technically, the operation was executed according to the contract’s code, yet it sparked widespread debate over whether the act should be considered a crime or merely exploitation of an existing loophole.
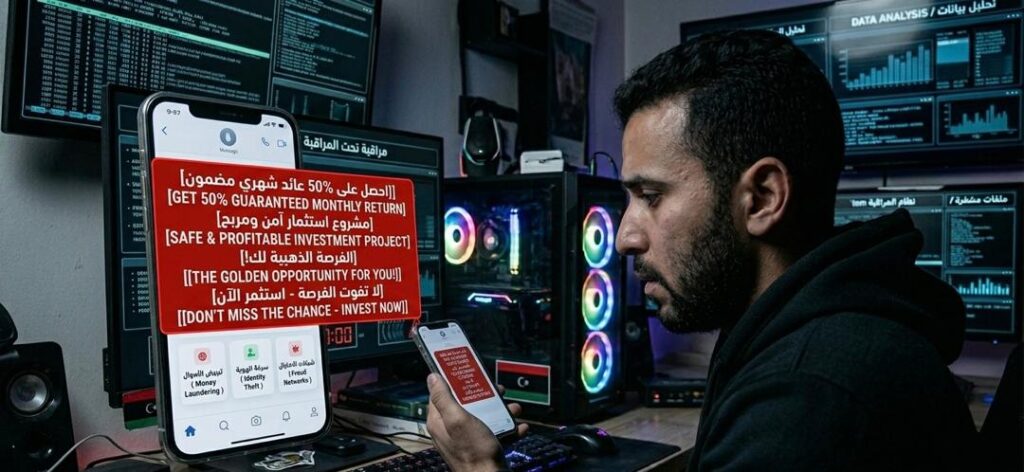
This incident represents one of the most dangerous emerging crimes in the digital business environment: Smart Contract Exploitation, where vulnerabilities in software code are used to execute unintended operations not anticipated by system developers, leading to severe financial losses.
Reports issued by Chainalysis indicated that attacks targeting smart contracts have increased significantly, especially with the rapid growth of Decentralized Finance (DeFi) platforms, which rely entirely on smart contracts to execute financial transactions.
First: Legal Challenges of Smart Contracts
From a legal perspective, this crime raises a fundamental issue concerning the legal nature of smart contracts. The central question is whether code itself should be considered legally binding law or whether it remains subject to traditional legal interpretation. Furthermore, exploiting a vulnerability may not always qualify as conventional hacking, making criminal classification more complex.
In this context, studies published by the European Parliament revealed that the absence of a clear legal framework governing smart contracts poses a significant challenge for regulatory authorities, particularly when determining legal liability after damages occur.
Reports from the World Economic Forum also confirmed that the decentralized economy faces increasing legal risks and that software vulnerabilities may evolve into tools for large-scale financial exploitation.
Second: Ethical and Islamic Legal Dimension
Within the framework of Islamic law, exploiting vulnerabilities for illegitimate financial gain is considered a form of unlawfully consuming the wealth of others, even in the absence of direct system intrusion. This reinforces the necessity of regulating such transactions through clear legal and ethical standards.
Third: Modern Technological Solutions
On the technical level, reports from ConsenSys emphasized that Smart Contract Auditing is one of the most effective methods for reducing these risks, as code is thoroughly examined before deployment to identify potential vulnerabilities.
Research conducted by the Massachusetts Institute of Technology (MIT) further demonstrated that automated code analysis tools can significantly reduce programming errors and minimize opportunities for exploitation.
Fourth: Analytical Conclusion
It becomes evident that Smart Contract Exploitation represents a highly complex legal and technological challenge that requires redefining concepts of responsibility and obligation within decentralized digital environments, while also balancing innovation with legal protection for investors and users.
Results
- Smart contracts create fertile ground for new forms of digital crimes.
- Exploiting vulnerabilities is not always classified as traditional cyber intrusion.
- The absence of legislation complicates legal prosecution of these acts.
- Resulting financial losses are immediate and often widespread.
- There is an urgent need to integrate legal frameworks with technological solutions.
Recommendations
- Develop a clear legal framework regulating smart contracts and decentralized transactions.
- Require platforms to conduct comprehensive security audits before deploying contracts.
- Strengthen cooperation between legal experts and developers in system design.
- Utilize advanced analytical tools for early vulnerability detection.
- Raise investor awareness regarding risks associated with smart contracts.
Open Question
With the increasing reliance on smart contracts, can “Code is Law” truly become a practical legal principle, or will legal intervention always remain essential to ensure justice and protect rights?
Sources
• Chainalysis reports on digital crimes
• European Parliament studies on smart contracts
• World Economic Forum reports on the decentralized economy
• ConsenSys reports on smart contract security
• Massachusetts Institute of Technology (MIT) research on software analysis
Smart Contracts, Smart Contract Exploitation, Decentralized Finance, DeFi, Blockchain Security, Digital Crimes, Software Vulnerabilities, Decentralized Economy, Smart Contract Hacking, Cybersecurity, Cryptocurrency, Blockchain Technology, Software Analysis, Financial Technology, Smart Contract Auditing, Investor Protection, Digital Financial Crimes, Legal Technology, Web3 Security, Blockchain Law, Crypto Regulation, Decentralized Systems, Cyber Risk, Digital Assets, FinTech Security, Crypto Compliance, Automated Code Analysis, Web3 Law, Digital Economy, Cryptocurrency Security
For more professional articles discussing similar topics, visit the articles section on our company website www.lawionyrs.com, which specializes in training, consulting, research, and publishing within an international legal framework. You can also explore accredited courses through the courses section, visual content through the video section, books through the books section, and additional services through the homepage by selecting the section that best suits your interests.